Earlier this month, the administrator of the cybercrime discussion board Breached obtained a cease-and-desist letter from a cybersecurity agency. The missive alleged that an public sale on the location for information stolen from 10 million clients of Mexico’s second-largest financial institution was faux information and harming the financial institution’s repute. The administrator responded to this empty menace by buying the stolen banking information and leaking it on the discussion board for everybody to obtain.
On August 3, 2022, somebody utilizing the alias “Holistic-K1ller” posted on Breached a thread promoting information allegedly stolen from Grupo Financiero Banorte, Mexico’s second-biggest monetary establishment by complete loans. Holistic-K1ller mentioned the database included the complete names, addresses, telephone numbers, Mexican tax IDs (RFC), e mail addresses and balances on greater than 10 million residents.
There was no purpose to consider Holistic-K1ller had fabricated their breach declare. This identification has been extremely energetic on Breached and its predecessor RaidForums for greater than two years, principally promoting databases from hacked Mexican entities. Final month, they bought buyer data on 36 million clients of the Mexican telephone firm Telcel; in March, they bought 33,000 pictures of Mexican IDs — with the entrance image and a selfie of every citizen. That very same month, in addition they bought information on 1.4 million clients of Mexican lending platform Yotepresto.
However this historical past was both ignored or ignored by Group-IB, the Singapore-based cybersecurity agency apparently employed by Banorte to assist reply to the information breach.
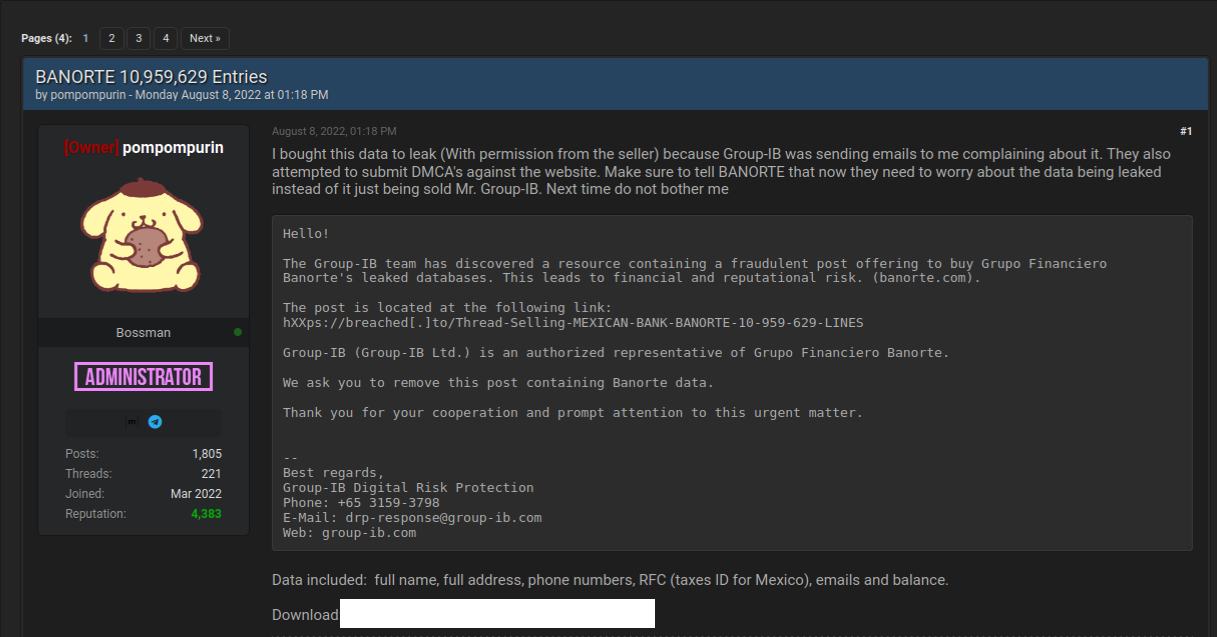
“The Group-IB staff has found a useful resource containing a fraudulent submit providing to purchase Grupo Financiero Banorte’s leaked databases,” reads a letter the Breach administrator mentioned they obtained from Group-IB. “We ask you to take away this submit containing Banorte information. Thanks in your cooperation and immediate consideration to this pressing matter.”
The administrator of Breached is “Pompompurin,” the identical particular person who alerted this writer in November 2021 to a obtrusive safety gap in a U.S. Justice Division web site that was used to spoof safety alerts from the FBI. In a submit to Breached on Aug. 8, Pompompurin mentioned they purchased the Banorte database from Hacker-K1ller’s gross sales thread as a result of Group-IB was sending emails complaining about it.
“Additionally they tried to submit DMCA’s towards the web site,” Pompompurin wrote, referring to authorized takedown requests below the Digital Millennium Copyright Act. “Ensure to inform Banorte that now they should fear in regards to the information being leaked as a substitute of simply being bought.”
Banorte didn’t reply to requests for remark. Nor did Group-IB. However in a short written assertion picked up on Twitter, Banorte mentioned there was no breach involving their infrastructure, and the information being bought is outdated.
“There was no violation of our platforms and technological infrastructure,” Banorte mentioned. “The set of data referred to is inaccurate and outdated, and doesn’t put our customers and clients in danger.”
That assertion could also be 100% true. Nonetheless, it’s troublesome to consider a greater instance of how not to do breach response. Banorte shrugging off this incident as a nothingburger is baffling: Whereas it’s virtually actually true that the financial institution steadiness data within the Banorte leak is now outdated, the remainder of the data (tax IDs, telephone numbers, e mail addresses) is more durable to vary.
“Is there one individual from our group that assume sending stop and desist letter to a hackers discussion board operator is a good suggestion?,” requested Ohad Zaidenberg, founding father of CTI League, a volunteer emergency response group that emerged in 2020 to assist struggle COVID-19 associated scams. “Who does it? As a substitute of serving to, they pushed the group from the hill.”
Kurt Seifried, director of IT for the CloudSecurityAlliance, was equally perplexed by the response to the Banorte breach.
“If the information wasn’t actual….did the financial institution assume a stop and desist would outcome within the itemizing being eliminated?” Seifried questioned on Twitter. “I imply, isn’t promoting breach information a worse crime normally than slander or libel? What was their thought course of?”
A extra typical response when a big financial institution suspects a breach is to strategy the vendor privately by way of an middleman to establish if the data is legitimate and what it may cost to take it off the market. Whereas it might appear odd to anticipate cybercriminals to make good on their claims to promote stolen information to just one celebration, eradicating bought stolen gadgets from stock is a reasonably primary perform of nearly all cybercriminal markets immediately (other than maybe websites that visitors in stolen identification information).
At a minimal, negotiating or just participating with a knowledge vendor should purchase the sufferer group extra time and clues with which to analyze the declare and ideally notify affected events of a breach earlier than the stolen information winds up on-line.
It’s true that a lot of hacked databases put up on the market on the cybercrime underground are bought solely after a small subset of in-the-know thieves have harvested the entire low-hanging fruit within the information — e.g., entry to cryptocurrency accounts or consumer credentials which are recycled throughout a number of web sites. And it’s actually not unparalleled for cybercriminals to return on their phrase and re-sell or leak data that they’ve bought beforehand.
However corporations within the throes of responding to a knowledge safety incident do themselves and clients no favors after they underestimate their adversaries, or attempt to intimidate cybercrooks with authorized threats. Such responses typically accomplish nothing, besides unnecessarily upping the stakes for everybody concerned whereas displaying a harmful naiveté about how the cybercrime underground works.

