Risk actors have revealed one more spherical of malicious packages to Python Package deal Index (PyPI) with the purpose of delivering information-stealing malware on compromised developer machines.
Curiously, whereas the malware goes by quite a lot of names like ANGEL Stealer, Celestial Stealer, Fade Stealer, Leaf $tealer, PURE Stealer, Devil Stealer, and @skid Stealer, cybersecurity firm Phylum discovered all of them to be copies of W4SP Stealer.
W4SP Stealer primarily features to siphon person knowledge, together with credentials, cryptocurrency wallets, Discord tokens, and different information of curiosity. It is created and revealed by an actor who goes by the aliases BillyV3, BillyTheGoat, and billythegoat356.
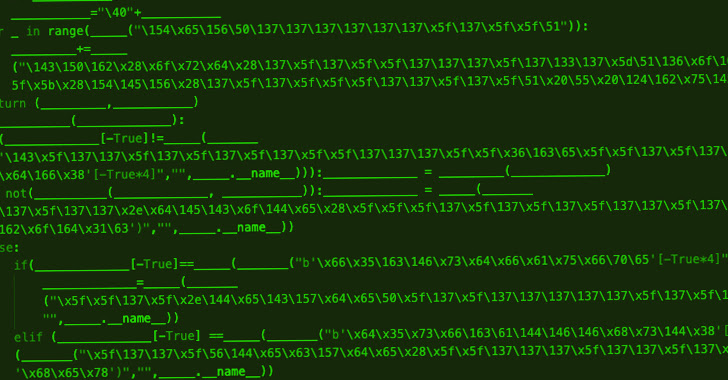
“For some purpose, every deployment seems to have merely tried to do a discover/substitute of the W4SP references in change for another seemingly arbitrary title,” the researchers mentioned in a report revealed earlier this week.
The 16 rogue modules are as follows: modulesecurity, informmodule, chazz, randomtime, proxygeneratorbil, easycordey, easycordeyy, tomproxies, sys-ej, py4sync, infosys, sysuptoer, nowsys, upamonkws, captchaboy, and proxybooster.
The marketing campaign distributing W4SP Stealer gained traction round October 2022, though indications are that it might have began way back to August 25, 2022. Since then dozens of extra bogus packages containing W4SP Stealer have been revealed on PyPI by the persistent menace actors.
The most recent iteration of the exercise, for what it is value, makes no apparent to cover its nefarious intentions, besides within the case of chazz, which leverages the package deal to obtain obfuscated Leaf $tealer malware hosted on the klgrth[.]io paste service.
It is value noting that earlier variations of the assault chains have additionally been noticed fetching next-stage Python code immediately from a public GitHub repository that then drops the credential stealer.
The surge in new copycat variants dovetails with GitHub’s takedown of the repository that held the unique W4SP Stealer supply code, indicating that cybercriminals doubtless not affiliated with the operation are additionally weaponizing the malware to assault PyPI customers.
“Open-source ecosystems comparable to PyPI, NPM, and the like are enormous straightforward targets for these sorts of actors to attempt to deploy this type of malware on,” the researchers mentioned. Their makes an attempt will solely turn into extra frequent, extra persistent, and most subtle.”
The software program provide chain safety agency, which saved tabs on the menace actor’s Discord channel, additional famous {that a} beforehand flagged package deal beneath the title of pystyle was trojanized by BillyTheGoat to distribute the stealer.
The module has not solely racked by 1000’s of downloads every month, but additionally began off as an innocuous utility in September 2021 to assist customers fashion console output. The malicious modifications have been launched in variations 2.1 and a couple of.2 launched on October 28, 2022.
These two variations, which have been stay on PyPI for about an hour earlier than they have been pulled, are alleged to have gotten 400 downloads, BillyTheGoat informed Phylum in an “unsolicited correspondence.”
“Simply because a package deal is benign in the present day and has proven a historical past of being benign for years doesn’t imply it should stay this fashion,” the researchers cautioned. “Risk actors have proven great persistence in constructing respectable packages, solely to poison them with malware after they’ve turn into sufficiently common.”