Authorities in the USA and United Kingdom right this moment levied monetary sanctions towards seven males accused of working “Trickbot,” a cybercrime-as-a-service platform primarily based in Russia that has enabled numerous ransomware assaults and checking account takeovers since its debut in 2016. The U.S. Division of the Treasury says the Trickbot group is related to Russian intelligence providers, and that this alliance led to the focusing on of many U.S. firms and authorities entities.
Initially a stealthy malicious program program delivered by way of e-mail and used to steal passwords, Trickbot developed into “a extremely modular malware suite that gives the Trickbot Group with the power to conduct a wide range of unlawful cyber actions, together with ransomware assaults,” the Treasury Division stated.
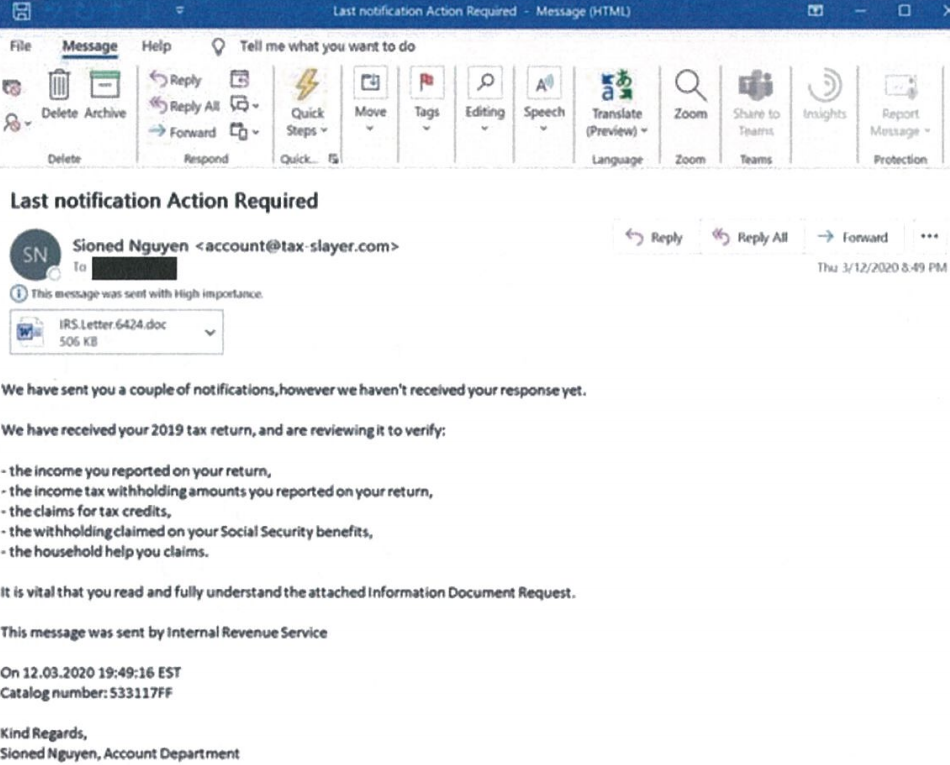
A spam e-mail from 2020 containing a Trickbot-infected attachment. Picture: Microsoft.
“Through the peak of the COVID-19 pandemic in 2020, Trickbot focused hospitals and healthcare facilities, launching a wave of ransomware assaults towards hospitals throughout the USA,” the sanctions discover continued. “In one among these assaults, the Trickbot Group deployed ransomware towards three Minnesota medical services, disrupting their pc networks and telephones, and inflicting a diversion of ambulances. Members of the Trickbot Group publicly gloated over the convenience of focusing on the medical services and the pace with which the ransoms have been paid to the group.”
Solely one of many males sanctioned right this moment is thought to have been criminally charged in reference to hacking exercise. In line with the Treasury Division, the alleged senior chief of the Trickbot group is 34-year-old Russian nationwide Vitaly “Bentley” Kovalev.
A New Jersey grand jury indicted Kovalev in 2012 after an investigation by the U.S. Secret Service decided that he ran a large “cash mule” scheme, which used phony job presents to trick folks into laundering cash stolen from hacked small to mid-sized companies in the USA. The 2012 indictment towards Kovalev pertains to cybercrimes he allegedly perpetrated previous to the creation of Trickbot.
BOTNET, THE MOVIE
In 2015, Kovalev reportedly started filming a film in Russia about cybercrime referred to as “Botnet.” In line with a 2016 story from Forbes.ru, Botnet’s opening scene was to depict the plight of Christina Svechinskaya, a Russian scholar arrested by FBI brokers in September 2010.

Christina Svechinskaya, a cash mule employed by Bentley who was arrested by the FBI in 2010.
Svechinskaya was one among Bentley’s cash mules, most of whom have been younger Russian college students on momentary journey visas in the USA. She was amongst 37 alleged mules charged with aiding a world cybercrime operation — mainly, organising phony company financial institution accounts for the only real objective of laundering stolen funds.
Though she possessed no actual hacking expertise, Svechinskaya’s mugshot and social media pictures went viral on-line and he or she was shortly dubbed “the world’s sexiest pc hacker” by the tabloids.
Kovalev’s Botnet movie mission was disrupted after Russian authorities raided the movie manufacturing firm’s workplaces as a part of a cybercrime investigation. In February 2016, Reuters reported that the raid was linked to a crackdown on “Dyre,” a classy trojan that U.S. federal investigators say was the precursor to the Trickbot malware. The Forbes.ru article cited sources near the investigation who stated the movie studio was working as a money-laundering entrance for the cybercrooks behind Dyre.
TREASON
However shifting political winds in Russia would quickly carry excessive treason expenses towards three of the Russian cybercrime investigators tied to the investigation into the movie studio. In a serious shakeup in 2017, the Kremlin levied treason expenses towards Sergey Mikhaylov, then deputy chief of Russia’s prime anti-cybercrime unit.
Additionally charged with treason was Ruslan Stoyanov, then a senior worker at Russian safety agency Kaspersky Lab [the Forbes.ru report from 2016 said investigators from Mikhaylov’s unit and Kaspersky Lab were present at the film company raid].
Russian media shops have speculated that the boys have been accused of treason for serving to American cybercrime investigators pursue prime Russian hackers. Nonetheless, the fees towards each males have been categorized and have by no means been formally revealed. After their transient, closed trial, each males have been convicted of treason. Mikhaylov was given a 22 12 months jail sentence; Stoyanov was sentenced to 14 years in jail.
In September 2021, the Kremlin issued treason expenses towards Ilya Sachkov, previously head of the cybersecurity agency Group-IB. In line with Reuters, Sachkov and his firm have been employed by the movie studio “to advise the Botnet director and writers on the finer factors of cybercrime.” Sachkov stays imprisoned in Russia pending his treason trial.
A WELL-OILED CYBERCRIME MACHINE
Trickbot was closely utilized by Conti and Ryuk, two of Russia’s most ruthless and profitable ransomware teams. Blockchain evaluation agency Chainalysis estimates that in 2021 alone, Conti extorted greater than USD $100 million from its hacking victims; Chainalysis estimates Ryuk extorted greater than USD $150 million from its ransomware victims.
The U.S. cybersecurity agency CrowdStrike has lengthy tracked the actions of Trickbot, Ryuk and Conti beneath the identical moniker — “Wizard Spider” — which CrowdStrike describes as “a Russia-nexus cybercriminal group behind the core growth and distribution of a classy arsenal of prison instruments, that enable them to run a number of various kinds of operations.”
“CrowdStrike Intelligence has noticed WIZARD SPIDER focusing on a number of international locations and industries corresponding to academia, power, monetary providers, authorities, and extra,” stated Adam Meyers, head of intelligence at CrowdStrike.
This isn’t the U.S. authorities’s first swipe on the Trickbot group. In early October 2020, KrebsOnSecurity broke the information that somebody had launched a sequence of coordinated assaults designed to disrupt the Trickbot botnet. Per week later, The Washington Put up ran a narrative saying the assault on Trickbot was the work of U.S. Cyber Command, a department of the Division of Protection headed by the director of the U.S. Nationwide Safety Company (NSA).
Days after Russia invaded Ukraine in February 2022, a Ukrainian researcher leaked a number of years of inner chat logs from the Conti ransomware gang. These candid conversations provide a captivating view into the challenges of operating a sprawling prison enterprise with greater than 100 salaried workers. Additionally they confirmed that Conti loved safety from prosecution by Russian authorities, so long as the hacker group took care to not goal Russian organizations.
As well as, the leaked Conti chats confirmed there was appreciable overlap within the operation and management of Conti, Trickbot and Ryuk.
Michael DeBolt, chief intelligence officer at cybersecurity agency Intel 471, stated the leaked Conti chats confirmed Bentley oversaw a crew of coders tasked with making certain that the Trickbot and Conti malware remained undetected by the totally different antivirus and safety software program distributors.
Within the years previous to the emergence of Trickbot in 2016, Bentley labored carefully on the Gameover ZeuS trojan, a peer-to-peer malware menace that contaminated between 500,000 and one million computer systems with an automatic ransomware pressure referred to as Cryptolocker, DeBolt stated.
The FBI has a standing $3 million bounty supplied for the seize of Evgeny “Slavik” Bogachev, the alleged creator of the Zeus trojan. And there are indications that Bentley labored immediately with Bogachev. DeBolt pointed to an October 2014 dialogue on the unique Russian hacking discussion board Mazafaka that included a grievance by a Russian internet hosting agency towards a discussion board person by the title “Ferrari” who had did not pay a $30,000 internet hosting invoice.
In that dialogue thread, it emerged that the internet hosting firm thought it was submitting a grievance towards Slavik. However the Mazafaka member who vouched for Ferrari’s membership on the discussion board stated they knew Ferrari as Bentley the mule handler, and sooner or later Slavik and Bentley should have been sharing the Ferrari person account.
“It’s doubtless that Slavik (aka. Bogachev) and Bentley (aka. Kovalev) shared the identical ‘Ferrari’ deal with on the Mazafaka discussion board circa 2014, which suggests the 2 had a working relationship at the moment, and helps the current US and UK Authorities bulletins concerning Kovalev’s previous involvement in cybercrime predating Dyre or the Trickbot Group,” DeBolt stated.
CrowdStrike’s Meyers stated whereas Wizard Spider operations have considerably lowered following the demise of Conti in June 2022, right this moment’s sanctions will doubtless trigger momentary disruptions for the cybercriminal group whereas they search for methods to avoid the monetary restrictions — which make it unlawful to transact with or maintain the property of sanctioned individuals or entities.
“Typically, when cybercriminal teams are disrupted, they may go darkish for a time solely to rebrand beneath a brand new title,” Meyers stated.
The prosecution of Kovalev is being dealt with by the U.S. Legal professional’s Workplace in New Jersey. A duplicate of the now-unsealed 2012 indictment of Kovalev is right here (PDF).

