A current scoop by Reuters revealed that cell apps for the U.S. Military and the Facilities for Illness Management and Prevention (CDC) have been integrating software program that sends customer information to a Russian firm known as Pushwoosh, which claims to be based mostly in the USA. However that story omitted an essential historic element about Pushwoosh: In 2013, one in every of its builders admitted to authoring the Pincer Trojan, malware designed to surreptitiously intercept and ahead textual content messages from Android cell gadgets.
Pushwoosh says it’s a U.S. based mostly firm that gives code for software program builders to profile smartphone app customers based mostly on their on-line exercise, permitting them to ship tailored notifications. However a current investigation by Reuters raised questions concerning the firm’s actual location and truthfulness.
The Military informed Reuters it eliminated an app containing Pushwoosh in March, citing “safety considerations.” The Military app was utilized by troopers at one of many nation’s major fight coaching bases.
Reuters mentioned the CDC likewise not too long ago eliminated Pushwoosh code from its app over safety considerations, after reporters knowledgeable the company Pushwoosh was not based mostly within the Washington D.C. space — as the corporate had represented — however was as a substitute operated from Novosibirsk, Russia.
Pushwoosh’s software program additionally was present in apps for “a wide selection of worldwide corporations, influential nonprofits and authorities companies from international client items firm Unilever and the Union of European Soccer Associations (UEFA) to the politically highly effective U.S. gun foyer, the Nationwide Rifle Affiliation (NRA), and Britain’s Labour Celebration.”
The corporate’s founder Max Konev informed Reuters Pushwoosh “has no reference to the Russian authorities of any variety” and that it shops its information in the USA and Germany.
However Reuters discovered that whereas Pushwoosh’s social media and U.S. regulatory filings current it as a U.S. firm based mostly variously in California, Maryland and Washington, D.C., the corporate’s staff are situated in Novosibirsk, Russia.
Reuters additionally discovered that the corporate’s handle in California doesn’t exist, and that two LinkedIn accounts for Pushwoosh staff in Washington, D.C. have been faux.
“Pushwoosh by no means talked about it was Russian-based in eight annual filings within the U.S. state of Delaware, the place it’s registered, an omission which may violate state regulation,” Reuters reported.
Pushwoosh admitted the LinkedIn profiles have been faux, however mentioned they have been created by a advertising agency to drum up enterprise for the corporate — not misrepresent its location.
Pushwoosh informed Reuters it used addresses within the Washington, D.C. space to “obtain enterprise correspondence” through the coronavirus pandemic. A evaluate of the Pushwoosh founder’s on-line presence by way of Constella Intelligence reveals his Pushwoosh e-mail handle was tied to a telephone quantity in Washington, D.C. that was additionally linked to e-mail addresses and account profiles for over a dozen different Pushwoosh staff.
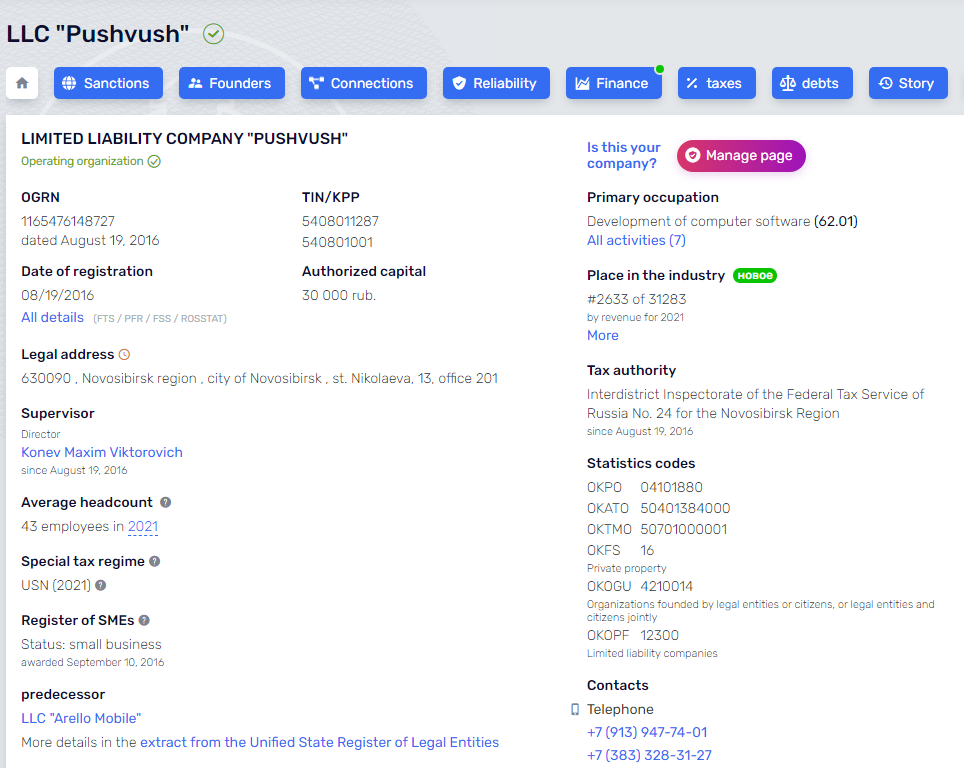
Pushwoosh was integrated in Novosibirsk, Russia in 2016.
THE PINCER TROJAN CONNECTION
The dust-up over Pushwoosh got here partly from information gathered by Zach Edwards, a safety researcher who till not too long ago labored for the Web Security Labs, a nonprofit group that funds analysis into on-line threats.
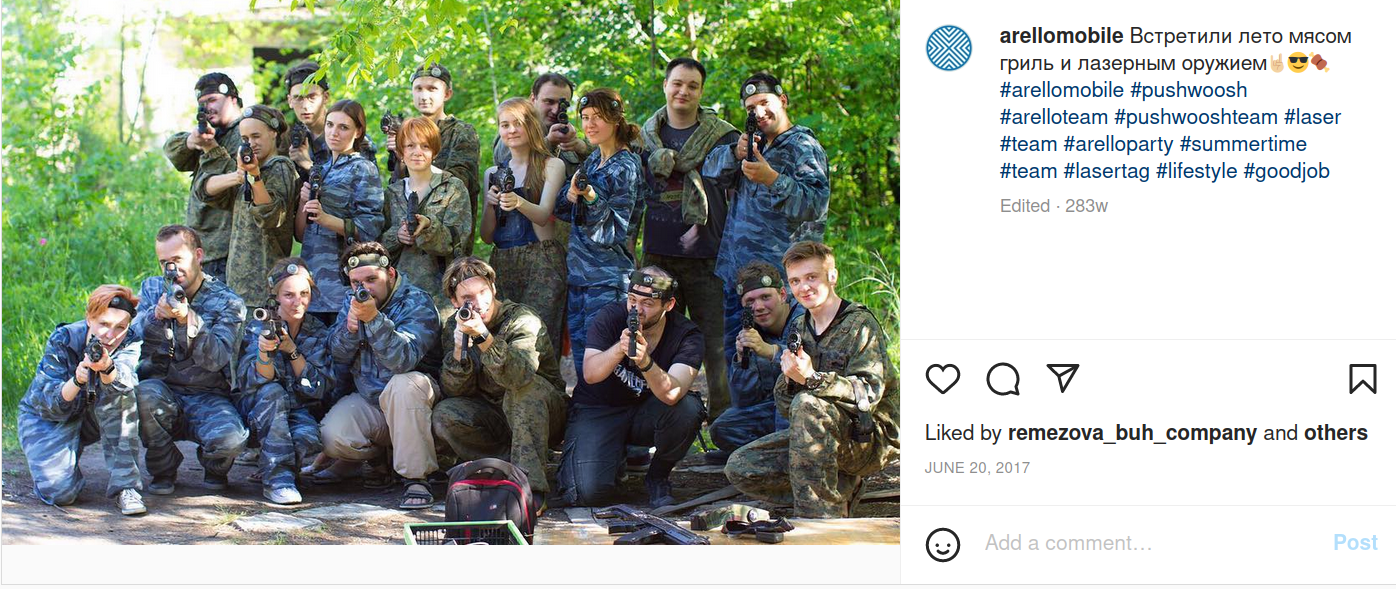
Edwards mentioned Pushwoosh started as Arello-Cell, and for a number of years the 2 co-branded — showing facet by facet at numerous know-how expos. Round 2016, he mentioned, the 2 corporations each began utilizing the Pushwoosh identify.
A search on Pushwoosh’s code base reveals that one of many firm’s longtime builders is a 41-year-old from Novosibirsk named Yuri Shmakov. In 2013, KrebsOnSecurity interviewed Shmakov for the story, “Who Wrote the Pincer Android Trojan?” whereby Shmakov acknowledged writing the malware as a contract challenge.
Shmakov informed me that, based mostly on the shopper’s specs, he suspected it would finally be put to nefarious makes use of. Even so, he accomplished the job and signed his work by together with his nickname within the app’s code.
“I used to be engaged on this app for some months, and I hoped that it will be actually useful,” Shmakov wrote. “[The] concept of this app is which you could set it up as a spam filter…block some calls and SMS remotely, from a Net service. I hoped that this can be [some kind of] blacklist, with logging about blocked [messages/calls]. However after all, I understood that shopper [did] probably not need this.”
Shmakov didn’t reply to requests for remark. His LinkedIn profile says he stopped working for Arello Cell in 2016, and that he presently is employed full-time because the Android staff chief at a web-based betting firm.
In a weblog submit responding to the Reuters story, Pushwoosh mentioned it’s a privately held firm integrated underneath the state legal guidelines of Delaware, USA, and that Pushwoosh Inc. was by no means owned by any firm registered within the Russian Federation.
“Pushwoosh Inc. used to outsource growth components of the product to the Russian firm in Novosibirsk, talked about within the article,” the corporate mentioned. “Nonetheless, in February 2022, Pushwoosh Inc. terminated the contract.”
Nonetheless, Edwards famous that dozens of developer subdomains on Pushwoosh’s major area nonetheless level to JSC Avantel, an Web supplier based mostly in Novosibirsk, Russia.
WAR GAMES
Edwards mentioned the U.S. Military’s app had a customized Pushwoosh configuration that didn’t seem on some other buyer implementation.
“It had an especially customized setup that existed nowhere else,” Edwards mentioned. “Initially, it was an in-app Net browser, the place it built-in a Pushwoosh javascript in order that any time a person clicked on hyperlinks, information went out to Pushwoosh they usually may push again no matter they wished by way of the in-app browser.”
An Military Instances article printed the day after the Reuters story ran mentioned a minimum of 1,000 folks downloaded the app, which “delivered updates for troops on the Nationwide Coaching Heart on Fort Irwin, Calif., a essential waypoint for deploying items to check their battlefield prowess earlier than heading abroad.”
In April 2022, roughly 4,500 Military personnel converged on the Nationwide Coaching Heart for a battle video games train on learn how to use classes discovered from Russia’s battle towards Ukraine to arrange for future fights towards a significant adversary resembling Russia or China.
Edwards mentioned regardless of Pushwoosh’s many prevarications, the corporate’s software program doesn’t seem to have performed something untoward to its prospects or customers.
“Nothing they did has been seen to be malicious,” he mentioned. “Apart from fully mendacity about the place they’re, the place their information is being hosted, and the place they’ve infrastructure.”
GOV 311
Edwards additionally discovered Pushwoosh’s know-how embedded in practically two dozen cell apps that have been bought to cities and cities throughout Illinois as a means to assist residents entry common details about their native communities and officers.
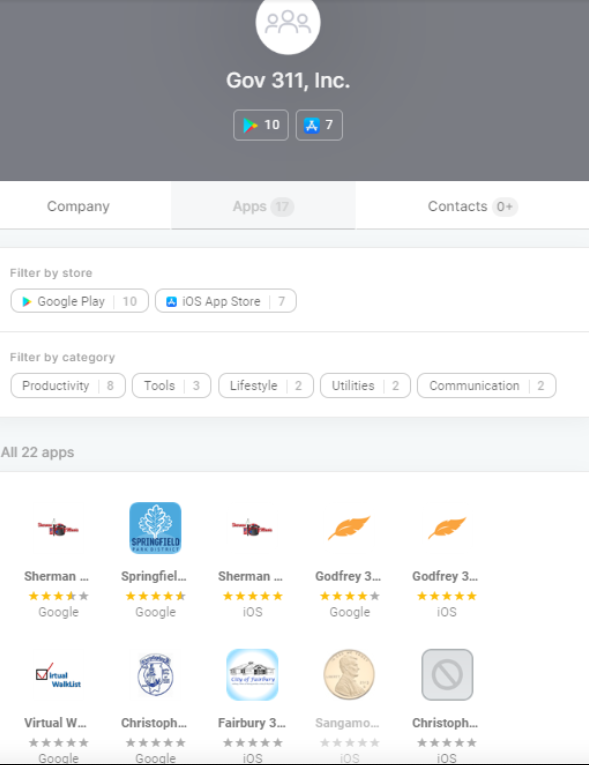 The Illinois apps that bundled Pushwoosh’s know-how have been produced by an organization known as Authorities 311, which is owned by Invoice McCarty, the present director of the Springfield Workplace of Price range and Administration. A 2014 story in The State Journal-Register mentioned Gov 311’s pricing was based mostly on inhabitants, and that the app would value round $2,500 per yr for a metropolis with roughly 25,000 folks.
The Illinois apps that bundled Pushwoosh’s know-how have been produced by an organization known as Authorities 311, which is owned by Invoice McCarty, the present director of the Springfield Workplace of Price range and Administration. A 2014 story in The State Journal-Register mentioned Gov 311’s pricing was based mostly on inhabitants, and that the app would value round $2,500 per yr for a metropolis with roughly 25,000 folks.
McCarty informed KrebsOnSecurity that his firm stopped utilizing Pushwoosh “years in the past,” and that it now depends by itself know-how to supply push notifications by way of its 311 apps.
However Edwards discovered a few of the 311 apps nonetheless attempt to telephone residence to Pushwoosh, such because the 311 app for Riverton, Ailing.
“Riverton ceased being a shopper a number of years in the past, which [is] in all probability why their app was by no means up to date to vary out Pushwoosh,” McCarty defined. “We’re within the strategy of updating all shopper apps and a web site refresh. As a part of that, previous unused apps like Riverton 311 can be deleted.”
FOREIGN ADTECH THREAT?
Edwards mentioned it’s removed from clear what number of different state and native authorities apps and Websites depend on know-how that sends person information to U.S. adversaries abroad. In July, Congress launched an amended model of the Intelligence Authorization Act for 2023, which included a brand new part specializing in information drawn from on-line advert auctions that might be used to geolocate people or achieve different details about them.
Enterprise Insider experiences that if this part makes it into the ultimate model — which the Senate additionally has to go — the Workplace for the Director of Nationwide Intelligence (ODNI) can have 60 days after the Act turns into regulation to supply a danger evaluation. The evaluation will look into “the counterintelligence dangers of, and the publicity of intelligence neighborhood personnel to, monitoring by overseas adversaries by way of promoting know-how information,” the Act states.
Edwards says he’s hoping these adjustments go, as a result of what he discovered with Pushwoosh is probably going only a drop in a bucket.
“I’m hoping that Congress acts on that,” he mentioned. “In the event that they have been to place a requirement that there’s an annual audit of dangers from overseas advert tech, that might a minimum of pressure folks to establish and doc these connections.”