Two U.S. males have been charged with hacking right into a U.S. Drug Enforcement Company (DEA) on-line portal that faucets into 16 completely different federal regulation enforcement databases. Each are alleged to be half of a bigger prison group that focuses on utilizing pretend emergency information requests from compromised police and authorities electronic mail accounts to publicly threaten and extort their victims.

Prosecutors for the Jap District of New York as we speak unsealed prison complaints in opposition to Sagar Steven Singh — also called “Weep” — a 19-year-old from Pawtucket, Rhode Island; and Nicholas Ceraolo, 25, of Queens, NY, who allegedly additionally glided by the handles “Convict” and “Ominus.”
The Justice Division says Singh and Ceraolo belong to a gaggle of cybercriminals recognized to its members as “ViLE,” who focus on acquiring private details about third-party victims, which they then use to harass, threaten or extort the victims, a apply often known as “doxing.”
“ViLE is collaborative, and the members routinely share ways and illicitly obtained info with one another,” prosecutors charged.
The federal government alleges the defendants and different members of ViLE use numerous strategies to acquire victims’ private info, together with:
-tricking customer support workers;
-submitting fraudulent authorized course of to social media corporations to elicit customers’ registration info;
-co-opting and corrupting company insiders;
-searching private and non-private on-line databases;
-accessing a nonpublic United States authorities database with out authorization
-unlawfully utilizing official electronic mail accounts belonging to different international locations.
The grievance says as soon as they obtained a sufferer’s info, Singh and Ceraolo would put up the data in a web-based discussion board. The federal government refers to this group solely as “Discussion board-1,” saying that it’s administered by the chief of ViLE (referenced within the grievance at CC-1).
“Victims are extorted into paying CC-1 to have their info faraway from Discussion board-1,” prosecutors allege. “Singh additionally makes use of the specter of revealing private info to extort victims into giving him entry to their social media accounts, which Singh then resells.”
Sources inform KrebsOnSecurity along with being members of ViLE, each Weep and Ominous are or had been workers members for Doxbin, a extremely poisonous on-line group that gives a discussion board for digging up private info on folks and posting it publicly. That is supported by the Doxin administrator’s claimed duty for a high-profile intrusion on the DEA’s regulation enforcement information sharing portal final 12 months.
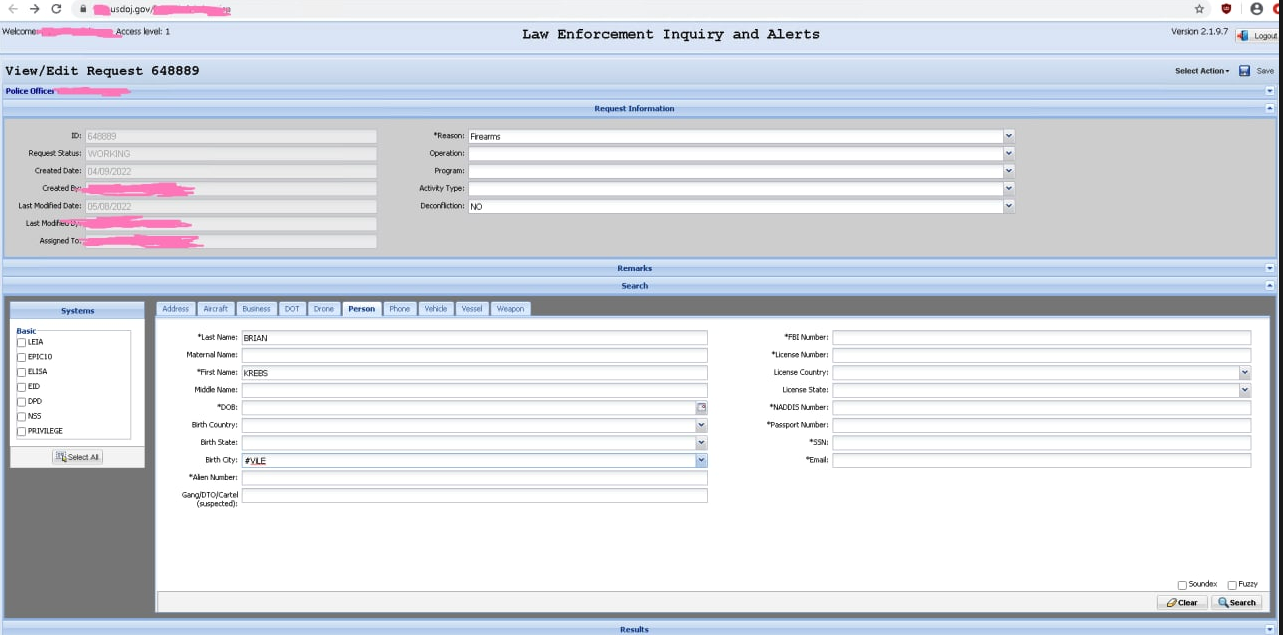
A screenshot of alleged entry to the Drug Enforcement Company’s intelligence sharing portal, shared by “KT,” the present administrator of the doxing and harassment group Doxbin.
The federal government alleges that on Might 7, 2022, Singh used stolen credentials to log right into a U.S. federal authorities portal with out authorization. The grievance doesn’t specify which company portal was hacked, nevertheless it does state that the portal included entry to regulation enforcement databases that monitor narcotics seizures in the USA.
On Might 12, 2022, KrebsOnSecurity broke the information that hackers had gained entry to a DEA portal that faucets into 16 completely different federal regulation enforcement databases. As reported on the time, the within scoop on how that hack went down got here from KT, the present administrator of the Doxbin and the person referenced within the authorities’s grievance as “CC-1.”
Certainly, a screenshot of the ViLE group web site consists of the group’s official roster, which lists KT on the high, adopted by Weep and Ominus.

A screenshot of the web site for the cybercriminal group “ViLE.” Picture: USDOJ.
In March 2022, KrebsOnSecurity warned that a number of cybercrime teams had been discovering success with fraudulent Emergency Information Requests (EDRs), whereby the hackers use compromised police and authorities electronic mail accounts to file warrantless information requests with social media companies and cellular telephony suppliers, testifying that the data being requested can’t look forward to a warrant as a result of it pertains to an pressing matter of life and dying.
That story confirmed that the earlier proprietor of the Doxbin additionally was a part of a teenage hacking group that specialised in providing pretend EDRs as a service on the darkish net.
Prosecutors say they tied Singh to the federal government portal hack as a result of he linked to it from an Web deal with that he’d beforehand used to entry a social media account registered in his title. Once they raided Singh’s residence on Sept. 8, 2022 and seized his gadgets, investigators with Homeland Safety discovered a mobile phone and laptop computer that allegedly “contained intensive proof of entry to the Portal.”
The grievance alleges that between February 2022 and Might 2022, Ceraolo used an official electronic mail account belonging to a Bangladeshi police official to pose as a police officer in communication with U.S.-based social media platforms.
“In these communications, Ceraolo requested private details about customers of those platforms, beneath the false pretense that the customers had been committing crimes or in life-threatening hazard,” the grievance states.
For instance, on or about March 13, 2022, Ceraolo allegedly used the Bangladeshi police electronic mail account to falsely declare that the goal of the EDR had despatched bomb threats, distributed little one pornography and threatened officers of the Bangladeshi authorities.
On or about Might 9, 2022, the federal government says, Singh despatched a pal screenshots of textual content messages between himself and somebody he had doxed on the Doxbin and was attempting to extort for his or her Instagram deal with. The information included the sufferer’s Social Safety quantity, driver’s license quantity, cellphone quantity, and residential deal with.
“Look acquainted?” Singh allegedly wrote to the sufferer. “You’re gonna comply to me when you don’t need something unfavourable to occur to your dad and mom. . . I’ve each element involving your dad and mom . . . permitting me to do no matter I want to them in malicious methods.”
Neither of the defendants may very well be instantly reached for remark. KT, the present administrator of the Doxbin, has not responded to requests for remark.
Ceraolo is a self-described safety researcher who has been credited in many information tales over time with discovering safety vulnerabilities at AT&T, T-Cellular, Comcast and Cox Communications.
Ceraolo’s said accomplice in most of those discoveries — a 30-year-old Connecticut man named Ryan “Phobia” Stevenson — was charged in 2019 with being a part of a gaggle that stole tens of millions of {dollars} price of cryptocurrencies through SIM-swapping, against the law that entails tricking a cellular supplier into routing a goal’s calls and textual content messages to a different gadget.
In 2018, KrebsOnSecurity detailed how Stevenson earned bug bounty rewards and public recognition from high telecom corporations for locating and reporting safety holes of their web sites, all of the whereas secretly peddling those self same vulnerabilities to cybercriminals.
In response to the Justice Division, if convicted Ceraolo faces as much as 20 years’ imprisonment for conspiracy to commit wire fraud; each Ceraolo and Singh face 5 years’ imprisonment for conspiracy to commit laptop intrusions.
A duplicate of the grievance in opposition to Ceraolo and Singh is right here (PDF).

