The U.S. Division of Justice (DOJ) at this time seized four-dozen domains that offered “booter” or “stresser” providers — companies that make it simple and low-cost for even non-technical customers to launch highly effective Distributed Denial of Service (DDoS) assaults designed knock targets offline. The DOJ additionally charged six U.S. males with laptop crimes associated to their alleged possession of the favored DDoS-for-hire providers.
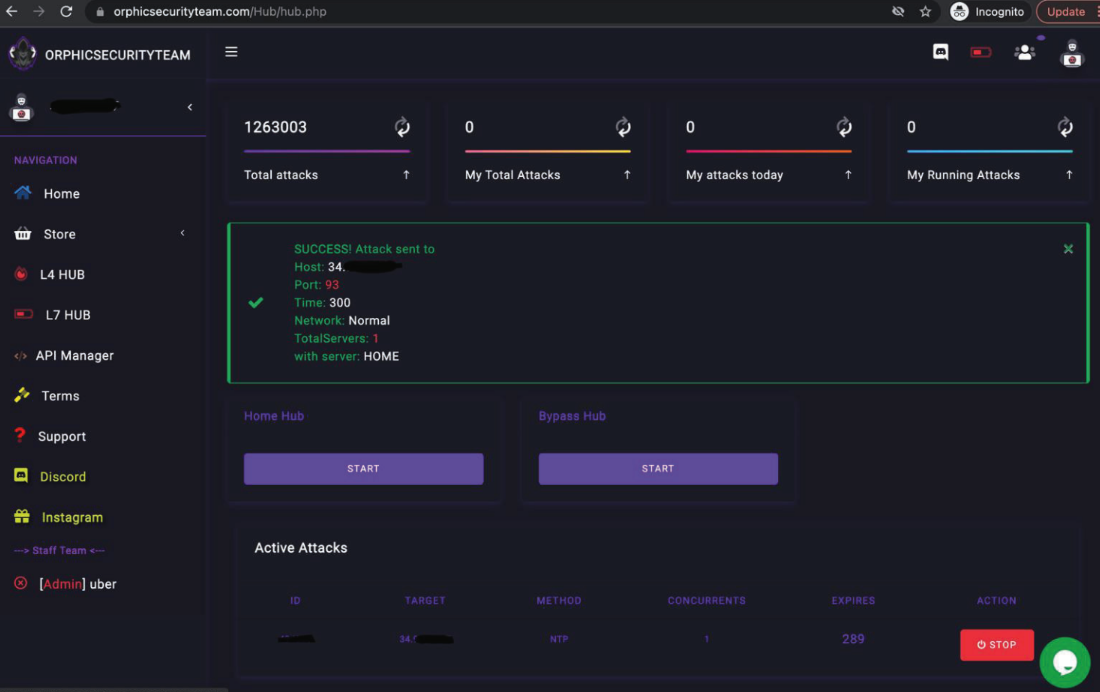
The booter service OrphicSecurityTeam[.]com was one of many 48 DDoS-for-hire domains seized by the Justice Division this week.
The DOJ mentioned the 48 domains it seized helped paying prospects launch thousands and thousands of digital sieges able to knocking Websites and even whole community suppliers offline.
Booter providers are marketed via a wide range of strategies, together with Darkish Internet boards, chat platforms and even youtube.com. They settle for fee by way of PayPal, Google Pockets, and/or cryptocurrencies, and subscriptions can vary in value from only a few {dollars} to a number of hundred per 30 days. The providers are typically priced in accordance with the quantity of visitors to be hurled on the goal, the length of every assault, and the variety of concurrent assaults allowed.
Prosecutors in Los Angeles say the booter websites supremesecurityteam[.]com and royalstresser[.]com have been the brainchild of Jeremiah Sam Evans Miller, a.ok.a. “John the Dev,” a 23-year-old from San Antonio, Texas. Miller was charged this week with conspiracy and violations of the Pc Fraud and Abuse Act (CFAA). The criticism in opposition to Miller alleges Royalstresser launched practically 200,000 DDoS assaults between November 2021 and February 2022.
Defendant Angel Manuel Colon Jr., a.ok.a Anonghost720 and Anonghost1337, is a 37-year-old from Belleview, Fla. Colon is suspected of working the booter service securityteam[.]io. He was additionally charged with conspiracy and CFAA violations. The feds say the SecurityTeam stresser service performed 1.3 million assaults between 2018 and 2022, and attracted some 50,000 registered customers.
Charged with conspiracy have been Corey Anthony Palmer, 22, of Lauderhill, Fla, for his alleged possession of booter[.]sx; and Shamar Shattock, 19, of Margate, Fla., for allegedly working the booter service astrostress[.]com, which had greater than 30,000 customers and blasted out some 700,000 assaults.
Two different alleged booter web site operators have been charged in Alaska. John M. Dobbs, 32, of Honolulu, HI is charged with aiding and abetting violations of the CFAA associated to the operation of IPStresser[.]com, which he allegedly ran for practically 13 years till final month. Throughout that point, IPstresser launched roughly 30 million DDoS assaults and garnered greater than two million registered customers.
Joshua Laing, 32, of Liverpool, NY, additionally was charged with CFAA infractions tied to his alleged possession of the booter service TrueSecurityServices[.]io, which prosecutors say had 18,000 customers and performed over 1.2 million assaults between 2018 and 2022.
Purveyors of stressers and booters declare they don’t seem to be answerable for how prospects use their providers, and that they aren’t breaking the legislation as a result of — like most safety instruments — stresser providers can be utilized for good or dangerous functions. For instance, the entire above-mentioned booter websites contained wordy “phrases of use” agreements that required prospects to agree they are going to solely stress-test their very own networks — and that they received’t use the service to assault others.
However the DOJ says these disclaimers often ignore the truth that most booter providers are closely reliant on continuously scanning the Web to commandeer misconfigured gadgets which might be essential for maximizing the scale and influence of DDoS assaults.
“None of those websites ever required the FBI to substantiate that it owned, operated, or had any property proper to the pc that the FBI attacked throughout its testing (as could be applicable if the assaults have been for a professional or licensed goal),” reads an affidavit (PDF) filed by Elliott Peterson, a particular agent within the FBI’s Anchorage discipline workplace.
“Moreover, evaluation of information associated to the FBI-initiated assaults revealed that the assaults launched by the SUBJECT DOMAINS concerned the in depth misuse of third-party providers,” Peterson continued. “Particularly, the entire examined providers supplied ‘amplification’ assaults, the place the assault visitors is amplified via unwitting third-party servers with a view to enhance the general assault dimension, and to shift the monetary burden of producing and transmitting all of that information away from the booter web site administrator(s) and onto third events.”
Based on U.S. federal prosecutors, the usage of booter and stresser providers to conduct assaults is punishable underneath each wire fraud legal guidelines and the Pc Fraud and Abuse Act (18 U.S.C. § 1030), and should lead to arrest and prosecution, the seizure of computer systems or different electronics, in addition to jail sentences and a penalty or nice.
The costs unsealed at this time stemmed from investigations launched by the FBI’s discipline workplaces in Los Angeles and Alaska, which spent months buying and testing assault providers supplied by the booter websites.
The same investigation initiating from the FBI’s Alaska discipline workplace in 2018 culminated in a takedown and arrest operation that focused 15 DDoS-for-hire websites, in addition to three booter retailer defendants who later pleaded responsible.
The Justice Division says its making an attempt to impress upon folks that even shopping for assaults from DDoS-for-hire providers can land Web customers in authorized jeopardy.
“Whether or not a prison launches an assault independently or pays a talented contractor to hold one out, the FBI will work with victims and use the appreciable instruments at our disposal to determine the individual or group accountable,” mentioned Donald Alway, the assistant director in command of the FBI’s Los Angeles discipline workplace.
The UK, which has been battling its fair proportion of home booter bosses, in 2020 began working on-line adverts aimed toward younger individuals who search the Internet for booter providers.
And in Europe, prosecutors have even gone after booter prospects.
Right here is the complete record of booter web site domains seized (or within the strategy of being seized) by the DOJ:
api-sky[.]xyz
astrostress[.]com
blackstresser[.]web
booter[.]sx
booter[.]vip
bootyou[.]web
brrsecurity[.]org
buuter[.]cc
cyberstress[.]us
defconpro[.]web
dragonstresser[.]com
dreams-stresser[.]io
exotic-booter[.]com
freestresser[.]so
instant-stresser[.]com
ipstress[.]org
ipstress[.]vip
ipstresser[.]com
ipstresser[.]us
ipstresser[.]wtf
ipstresser[.]xyz
kraysec[.]com
mcstorm[.]io
nightmarestresser[.]com
orphicsecurityteam[.]com
ovhstresser[.]com
quantum-stresser[.]web
redstresser[.]cc
royalstresser[.]com
securityteam[.]io
shock-stresser[.]com
silentstress[.]web
stresser[.]app
stresser[.]greatest
stresser[.]gg
stresser[.]is
stresser[.]web/stresser[.]org
stresser[.]one
stresser[.]store
stresser[.]so
stresser[.]high
stresserai[.]com
sunstresser[.]com
supremesecurityteam[.]com
truesecurityservices[.]io
vdos-s[.]co
zerostresser[.]com

