A safety researcher was awarded a bug bounty of $107,500 for figuring out safety points in Google Dwelling sensible audio system that may very well be exploited to put in backdoors and switch them into wiretapping units.
The issues “allowed an attacker inside wi-fi proximity to put in a ‘backdoor’ account on the machine, enabling them to ship instructions to it remotely over the web, entry its microphone feed, and make arbitrary HTTP requests throughout the sufferer’s LAN,” the researcher, who goes by the identify Matt, disclosed in a technical write-up printed this week.
In making such malicious requests, not solely may the Wi-Fi password get uncovered, but in addition present the adversary direct entry to different units linked to the identical community. Following accountable disclosure on January 8, 2021, the problems have been remediated by Google in April 2021.
The issue, in a nutshell, has to do with how the Google Dwelling software program structure could be leveraged so as to add a rogue Google person account to a goal’s dwelling automation machine.
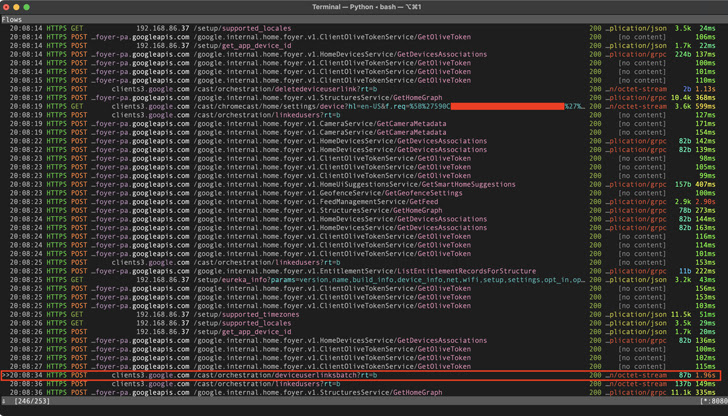
In an assault chain detailed by the researcher, a menace actor trying to snoop on a sufferer can trick the person into putting in a malicious Android app, which, upon detecting a Google Dwelling machine on the community, points stealthy HTTP requests to hyperlink an attacker’s account to the sufferer’s machine.
Taking issues a notch greater, it additionally emerged that, by staging a Wi-Fi deauthentication assault to drive a Google Dwelling machine to disconnect from the community, the equipment could be made to enter a “setup mode” and create its personal open Wi-Fi community.
The menace actor can subsequently connect with the machine’s setup community and request particulars like machine identify, cloud_device_id, and certificates, and use them to hyperlink their account to the machine.
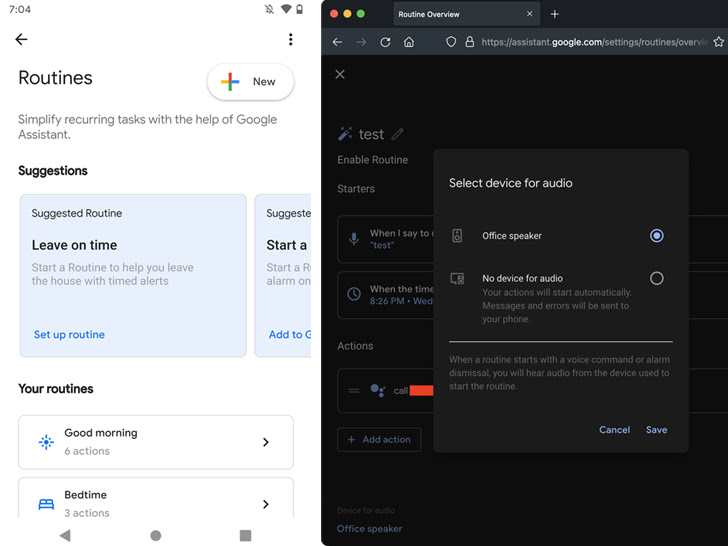
Whatever the assault sequence employed, a profitable hyperlink course of permits the adversary to benefit from Google Dwelling routines to show down the quantity to zero and name a particular telephone quantity at any given time limit to spy on the sufferer by means of the machine’s microphone.
“The one factor the sufferer might discover is that the machine’s LEDs flip strong blue, however they’d most likely simply assume it is updating the firmware or one thing,” Matt mentioned. “Throughout a name, the LEDs don’t pulse like they usually do when the machine is listening, so there is no such thing as a indication that the microphone is open.”
Moreover, the assault could be prolonged to make arbitrary HTTP requests throughout the sufferer’s community and even learn information or introduce malicious modifications on the linked machine that will get utilized after a reboot.
This isn’t the primary time such assault strategies have been devised to covertly listen in on potential targets by means of voice-activated units.
In November 2019, a gaggle of teachers disclosed a way referred to as Mild Instructions, which refers to a vulnerability of MEMS microphones that allows attackers to remotely inject inaudible and invisible instructions into standard voice assistants like Google Assistant, Amazon Alexa, Fb Portal, and Apple Siri utilizing gentle.