Ransomware teams are continually devising new strategies for infecting victims and convincing them to pay up, however a few methods examined not too long ago appear particularly devious. The primary facilities on focusing on healthcare organizations that supply consultations over the Web and sending them booby-trapped medical information for the “affected person.” The opposite entails fastidiously enhancing electronic mail inboxes of public firm executives to make it seem that some have been concerned in insider buying and selling.

Alex Holden is founding father of Maintain Safety, a Milwaukee-based cybersecurity agency. Holden’s staff gained visibility into discussions amongst members of two totally different ransom teams: CLOP (a.okay.a. “Cl0p” a.okay.a. “TA505“), and a more recent ransom group often called Venus.
Final month, the U.S. Division of Well being and Human Companies (HHS) warned that Venus ransomware assaults have been focusing on plenty of U.S. healthcare organizations. First noticed in mid-August 2022, Venus is understood for hacking into victims’ publicly-exposed Distant Desktop providers to encrypt Home windows units.
Holden stated the inner discussions among the many Venus group members point out this gang has no downside having access to sufferer organizations.
“The Venus group has issues getting paid,” Holden stated. “They’re focusing on a variety of U.S. firms, however no one desires to pay them.”
Which could clarify why their newest scheme facilities on making an attempt to border executives at public firms for insider buying and selling expenses. Venus indicated it not too long ago had success with a technique that entails fastidiously enhancing a number of electronic mail inbox recordsdata at a sufferer agency — to insert messages discussing plans to commerce giant volumes of the corporate’s inventory primarily based on personal info.
“We imitate correspondence of the [CEO] with a sure insider who shares monetary experiences of his firms by means of which your sufferer allegedly trades within the inventory market, which naturally is a felony offense and — in line with US federal legal guidelines [includes the possibility of up to] 20 years in jail,” one Venus member wrote to an underling.
“You want to create this file and inject into the machine(s) like this in order that metadata would say that they have been created on his laptop,” they continued. “One among my shoppers did it, I don’t understand how. Along with pst, it’s good to decompose a number of recordsdata into totally different locations, in order that metadata says the recordsdata are native from a sure date and time somewhat than created yesterday on an unknown machine.”
Holden stated it’s not simple to plant emails into an inbox, however it may be carried out with Microsoft Outlook .pst recordsdata, which the attackers might also have entry to in the event that they’d already compromised a sufferer community.
“It’s not going to be forensically stable, however that’s not what they care about,” he stated. “It nonetheless has the potential to be an enormous scandal — at the very least for some time — when a sufferer is being threatened with the publication or launch of those information.”
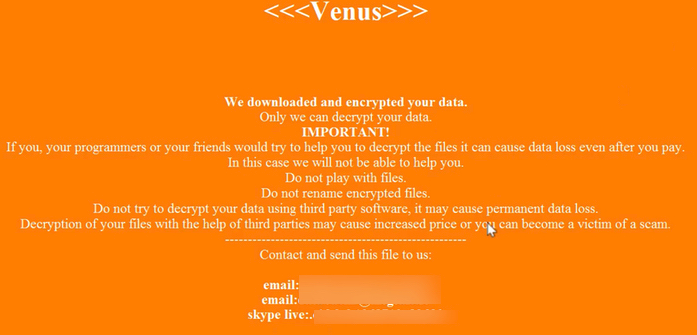
The Venus ransom group’s extortion be aware. Picture: Tripwire.com
Holden stated the CLOP ransomware gang has a unique downside of late: Not sufficient victims. The intercepted CLOP communication seen by KrebsOnSecurity exhibits the group bragged about twice having success infiltrating new victims within the healthcare trade by sending them contaminated recordsdata disguised as ultrasound photographs or different medical paperwork for a affected person searching for a distant session.
The CLOP members stated one tried-and-true technique of infecting healthcare suppliers concerned gathering healthcare insurance coverage and cost information to make use of in submitting requests for a distant session on a affected person who has cirrhosis of the liver.
“Mainly, they’re relying on docs or nurses reviewing the affected person’s chart and scans simply earlier than the appointment,” Holden stated. “They initially mentioned stepping into with cardiovascular points, however determined cirrhosis or fibrosis of the liver can be extra prone to be diagnosable remotely from current check outcomes and scans.”
Whereas CLOP as a cash making collective is a reasonably younger group, safety specialists say CLOP members hail from a gaggle of Risk Actors (TA) often called “TA505,” which MITRE’s ATT&CK database says is a financially motivated cybercrime group that has been lively since at the very least 2014. “This group is understood for regularly altering malware and driving international developments in felony malware distribution,” MITRE assessed.
In April, 2021, KrebsOnSecurity detailed how CLOP helped pioneer one other innovation geared toward pushing extra victims into paying an extortion demand: Emailing the ransomware sufferer’s prospects and companions instantly and warning that their information can be leaked to the darkish internet until they’ll persuade the sufferer agency to pay up.
Safety agency Tripwire factors out that the HHS advisory on Venus says a number of menace actor teams are probably distributing the Venus ransomware. Tripwire’s ideas for all organizations on avoiding ransomware assaults embody:
- Making safe offsite backups.
- Operating up-to-date safety options and making certain that your computer systems are protected with the most recent safety patches towards vulnerabilities.
- Utilizing hard-to-crack distinctive passwords to guard delicate information and accounts, in addition to enabling multi-factor authentication.
- Encrypting delicate information wherever attainable.
- Repeatedly educating and informing workers concerning the dangers and strategies utilized by cybercriminals to launch assaults and steal information.
Whereas the above ideas are essential and helpful, one important space of ransomware preparedness neglected by too many organizations is the necessity to develop — after which periodically rehearse — a plan for the way everybody within the group ought to reply within the occasion of a ransomware or information ransom incident. Drilling this breach response plan is essential as a result of it helps expose weaknesses in these plans that could possibly be exploited by the intruders.
As famous in final 12 months’s story Don’t Wanna Pay Ransom Gangs? Check Your Backups, specialists say the largest cause ransomware targets and/or their insurance coverage suppliers nonetheless pay after they have already got dependable backups of their methods and information is that no one on the sufferer group bothered to check prematurely how lengthy this information restoration course of would possibly take.
“Out of the blue the sufferer notices they’ve a few petabytes of information to revive over the Web, and so they notice that even with their quick connections it’s going to take three months to obtain all these backup recordsdata,” stated Fabian Wosar, chief know-how officer at Emsisoft. “Lots of IT groups by no means really make even a back-of-the-napkin calculation of how lengthy it will take them to revive from an information price perspective.”

