Picture: Shutterstock.
A cybersecurity agency says it has intercepted a big, distinctive stolen knowledge set containing the names, addresses, electronic mail addresses, cellphone numbers, Social Safety Numbers and dates of delivery on practically 23 million Individuals. The agency’s evaluation of the info suggests it corresponds to present and former clients of AT&T. The telecommunications large stopped wanting saying the info wasn’t theirs, but it surely maintains the information don’t seem to have come from its methods and could also be tied to a earlier knowledge incident at one other firm.
Milwaukee-based cybersecurity consultancy Maintain Safety stated it intercepted a 1.6 gigabyte compressed file on a well-liked darkish net file-sharing website. The most important merchandise within the archive is a 3.6 gigabyte file referred to as “dbfull,” and it incorporates 28.5 million information, together with 22.8 million distinctive electronic mail addresses and 23 million distinctive SSNs. There aren’t any passwords within the database.
Maintain Safety founder Alex Holden stated quite a lot of patterns within the knowledge recommend it pertains to AT&T clients. For starters, electronic mail addresses ending in “att.internet” accounted for 13.7 % of all addresses within the database, with addresses from SBCGLobal.internet and Bellsouth.internet — each AT&T firms — making up one other seven %. In distinction, Gmail customers made up greater than 30 % of the info set, with Yahoo addresses accounting for twenty-four %. Greater than 10,000 entries within the database listing “none@att.com” within the electronic mail discipline.
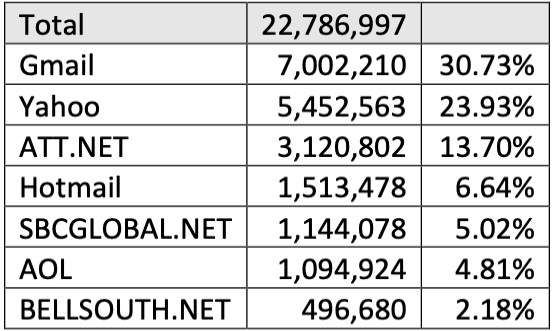
Maintain Safety discovered these electronic mail domains account for 87% of all domains within the knowledge set. Practically 21% belonged to AT&T clients.
Holden’s workforce additionally examined the variety of electronic mail information that included an alias within the username portion of the e-mail, and located 293 electronic mail addresses with plus addressing. Of these, 232 included an alias that indicated the shopper had signed up at some AT&T property; 190 of the aliased electronic mail addresses have been “+att@”; 42 have been “+uverse@,” an oddly particular reference to a DirecTV/AT&T entity that included broadband Web. In September 2016, AT&T rebranded U-verse as AT&T Web.
In keeping with its web site, AT&T Web is obtainable in 21 states, together with Alabama, Arkansas, California, Florida, Georgia, Indiana, Kansas, Kentucky, Louisiana, Michigan, Missouri, Nevada, North Carolina, Ohio, Oklahoma, Tennessee, Texas and Wisconsin. Practically all the information within the database that comprise a state designation corresponded to these 21 states; all different states made up simply 1.64 % of the information, Maintain Safety discovered.
Picture: Maintain Safety.
The overwhelming majority of information on this database belong to shoppers, however nearly 13,000 of the entries are for company entities. Holden stated 387 of these company names began with “ATT,” with numerous entries like “ATT PVT XLOW” showing 81 occasions. And many of the addresses for these entities are AT&T company places of work.
How previous is that this knowledge? One clue could also be within the dates of delivery uncovered on this database. There are only a few information on this file with dates of delivery after 2000.
“Primarily based on these statistics, we see that the final vital variety of subscribers born in March of 2000,” Holden advised KrebsOnSecurity, noting that AT&T requires new account holders to be 18 years of age or older. “Subsequently, it is smart that the dataset was probably created near March of 2018.”
There was additionally this anomaly: Holden stated considered one of his analysts is an AT&T buyer with a 13-letter final title, and that her AT&T invoice has at all times had the identical distinctive misspelling of her surname (they added yet one more letter). He stated the analyst’s title is identically misspelled on this database.
KrebsOnSecurity shared the big knowledge set with AT&T, in addition to Maintain Safety’s evaluation of it. AT&T finally declined to say whether or not all the folks within the database are or have been in some unspecified time in the future AT&T clients. The corporate stated the info seems to be a number of years previous, and that “it’s not instantly potential to find out the proportion that could be clients.”
“This data doesn’t seem to have come from our methods,” AT&T stated in a written assertion. “It could be tied to a earlier knowledge incident at one other firm. It’s unlucky that knowledge can proceed to floor over a number of years on the darkish net. Nonetheless, clients typically obtain notices after such incidents, and recommendation for ID theft is constant and might be discovered on-line.”
The corporate declined to elaborate on what they meant by “a earlier knowledge incident at one other firm.”
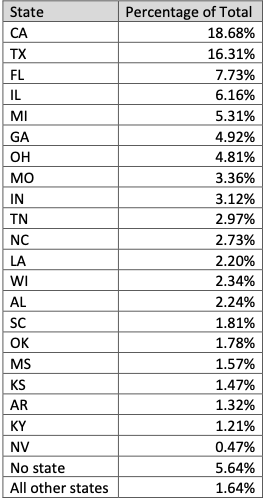
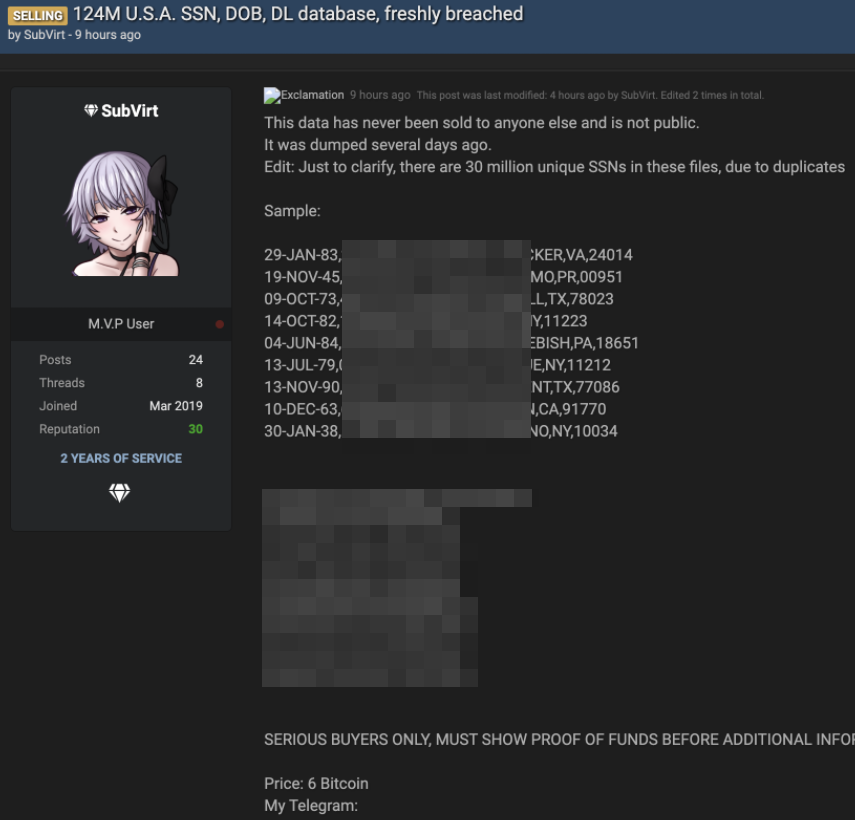
But it surely appears probably that this database is expounded to at least one that went up on the market on a hacker discussion board on August 19, 2021. That public sale ran with the title “AT&T Database +70M (SSN/DOB),” and was supplied by ShinyHunters, a well known risk actor with a protracted historical past of compromising web sites and developer repositories to steal credentials or API keys.
Picture: BleepingComputer
ShinyHunters established the beginning value for the public sale at $200,000, however set the “flash” or “purchase it now” value at $1 million. The public sale additionally included a small sampling of the stolen data, however that pattern is not obtainable. The hacker discussion board the place the ShinyHunters gross sales thread existed was seized by the FBI in April, and its alleged administrator arrested.
However cached copies of the public sale, as recorded by cyber intelligence agency Intel 471, present ShinyHunters obtained bids of as much as $230,000 for your complete database earlier than they suspended the sale.
“This thread has been deleted a number of occasions,” ShinyHunters wrote of their public sale dialogue on Sept. 6, 2021. “Subsequently, the public sale is suspended. AT&T can be obtainable on WHM as quickly as they settle for new distributors.”
The WHM initialism was a reference to the White Home Market, a darkish net market that shut down in October 2021.
“In lots of circumstances, when a database will not be bought, ShinyHunters will launch it at no cost on hacker boards,” wrote BleepingComputer’s Lawrence Abrams, who broke the information of the public sale final yr and confronted AT&T concerning the hackers’ claims.
AT&T gave Abrams an analogous assertion, saying the info didn’t come from their methods.
“When requested whether or not the info might have come from a third-party companion, AT&T selected to not speculate,” Abrams wrote. “‘Given this data didn’t come from us, we will’t speculate on the place it got here from or whether or not it’s legitimate,’” AT&T advised BleepingComputer.
Requested to reply to AT&T’s denial, ShinyHunters advised BleepingComputer on the time, “I don’t care in the event that they don’t admit. I’m simply promoting.”
On June 1, 2022, a 21-year-old Frenchman was arrested in Morocco for allegedly being a member of ShinyHunters. Databreaches.internet experiences the defendant was arrested on an Interpol “Crimson Discover” on the request of a U.S. federal prosecutor from Washington state.
Databreaches.internet suggests the warrant may very well be tied to a ShinyHunters theft in Might 2020, when the group introduced that they had exfiltrated 500 GB of Microsoft’s supply code from Microsoft’s non-public GitHub repositories.
“Researchers assess that Shiny Hunters gained entry to roughly 1,200 non-public repositories round March 28, 2020, which have since been secured,” reads a Might 2020 alert posted by the New Jersey Cybersecurity & Communications Integration Cell, a element inside the New Jersey Workplace of Homeland Safety and Preparedness.
“Although the breach was largely dismissed as insignificant, some photographs of the listing itemizing seem to comprise supply code for Azure, Workplace, and a few Home windows runtimes, and considerations have been raised concerning entry to personal API keys or passwords that will have been mistakenly included in some non-public repositories,” the alert continues. “Moreover, Shiny Hunters is flooding darkish net marketplaces with breached databases.”
Final month, T-Cell agreed to pay $350 million to settle a consolidated class motion lawsuit over a breach in 2021 that affected 40 million present and former clients. The breach got here to mild on Aug. 16, 2021, when somebody beginning promoting tens of hundreds of thousands of SSN/DOB information from T-Cell on the identical hacker discussion board the place the ShinyHunters would submit their public sale for the claimed AT&T database simply three days later.
T-Cell has not disclosed many particulars concerning the “how” of final yr’s breach, but it surely stated the intruder(s) “leveraged their information of technical methods, together with specialised instruments and capabilities, to achieve entry to our testing environments after which used brute pressure assaults and different strategies to make their manner into different IT servers that included buyer knowledge.”
A gross sales thread tied to the stolen T-Cell buyer knowledge.

