Two long-running surveillance campaigns have been discovered concentrating on the Uyghur group in China and elsewhere with Android adware instruments designed to reap delicate data and observe their whereabouts.
This encompasses a beforehand undocumented malware pressure referred to as BadBazaar and up to date variants of an espionage artifact dubbed MOONSHINE by researchers from the College of Toronto’s Citizen Lab in September 2019.
“Cell surveillance instruments like BadBazaar and MOONSHINE can be utilized to trace lots of the ‘pre-criminal’ actions, actions thought-about indicative of non secular extremism or separatism by the authorities in Xinjiang,” Lookout stated in an in depth write-up of the operations.
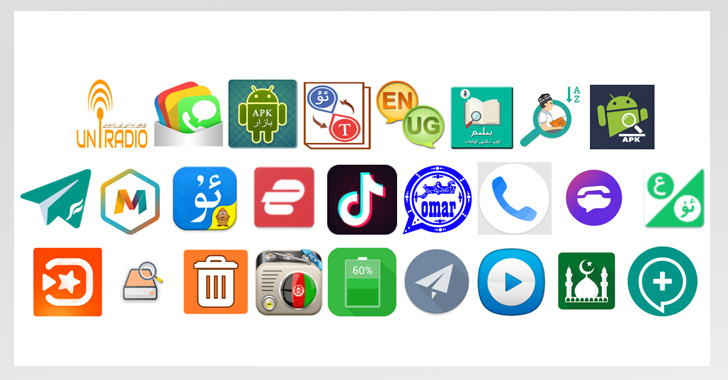
The BadBazaar marketing campaign, in line with the safety agency, is alleged thus far way back to late 2018 and comprise 111 distinctive apps that masquerade as benign video gamers, messengers, non secular apps, and even TikTok.
Whereas these samples had been distributed via Uyghur-language social media platforms and communication channels, Lookout famous it discovered a dictionary app named “Uyghur Lughat” on the Apple App Retailer that communicates with a server utilized by its Android counterpart to collect fundamental iPhone data.
The iOS app continues to be obtainable on the App Retailer.
“Since BadBazaar variants typically purchase their surveillance capabilities by downloading updates from their [command-and-control server], it’s attainable the menace actor is hoping to later replace the iOS pattern with comparable surveillance performance,” the researchers identified.
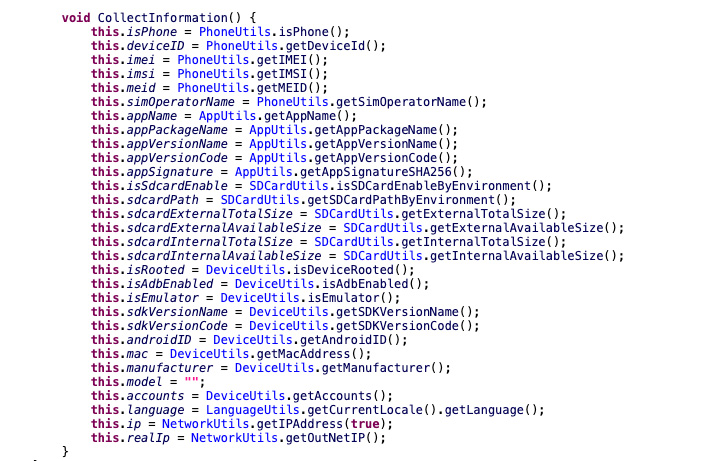
BadBazaar, as soon as put in, comes with a number of options that enable it to gather name logs, GPS places, SMS messages, and recordsdata of curiosity; document cellphone calls; take photos; and exfiltrate substantial system metadata.
Additional evaluation of BadBazaar’s infrastructure has revealed overlaps with one other adware operation aimed on the ethnic minority that got here to mild in July 2020 and which made use of an Android toolset referred to as DoubleAgent.
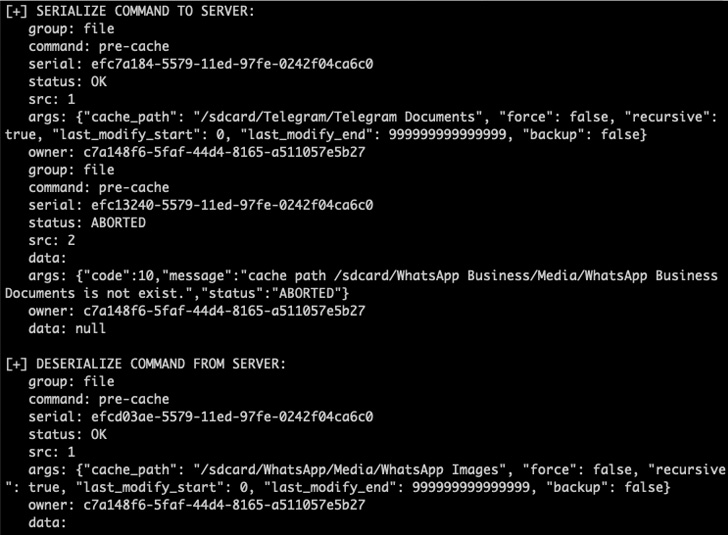
Assaults using MOONSHINE, in an identical vein, have employed over 50 malicious apps since July 2022 which can be engineered to amass private knowledge from the contaminated units, along with recording audio and downloading arbitrary recordsdata.
“The vast majority of these samples are trojanized variations of common social media platforms, like WhatsApp or Telegram, or trojanized variations of Muslim cultural apps, Uyghur-language instruments, or prayer apps,” the researchers stated.
Prior malicious cyber actions leveraging the MOONSHINE Android adware package have been attributed to a menace actor tracked as POISON CARP (aka Evil Eye or Earth Empusa), a China-based nation-state collective recognized for its assaults in opposition to Uyghurs.
The findings come just a little over a month after Verify Level disclosed particulars of one other long-standing surveillanceware operation aimed on the Turkic Muslim group that deployed a trojan named MobileOrder since at the least 2015.
“BadBazaar and these new variants of MOONSHINE add to the already intensive assortment of distinctive surveillanceware utilized in campaigns to surveil and subsequently detain people in China,” Lookout stated.
“The large distribution of each BadBazaar and MOONSHINE, and the speed at which new performance has been launched point out that improvement of those households is ongoing and that there’s a continued demand for these instruments.”
The event additionally follows a report from Google Mission Zero final week, which uncovered proof of an unnamed business surveillance vendor weaponizing three zero-day safety flaws in Samsung telephones with an Exynos chip operating kernel model 4.14.113. The safety holes had been plugged by Samsung in March 2021.
That stated, the search big stated the exploitation mirrored a sample just like current compromises the place malicious Android apps had been abused to focus on customers in Italy and Kazakhstan with an implant known as Hermit, which has been linked to Italian firm RCS Lab.