Microsoft’s resolution to block Visible Primary for Functions (VBA) macros by default for Workplace recordsdata downloaded from the web has led many menace actors to improvise their assault chains in latest months.
Now in keeping with Cisco Talos, superior persistent menace (APT) actors and commodity malware households alike are more and more utilizing Excel add-in (.XLL) recordsdata as an preliminary intrusion vector.
Weaponized Workplace paperwork delivered through spear-phishing emails and different social engineering assaults have remained one of many broadly used entry factors for legal teams seeking to execute malicious code.
These paperwork historically immediate the victims to allow macros to view seemingly innocuous content material, solely to activate the execution of malware stealthily within the background.
To counter this misuse, the Home windows maker enacted a vital change beginning in July 2022 that blocks macros in Workplace recordsdata connected to electronic mail messages, successfully severing a vital assault vector.
Whereas this blockade solely applies to new variations of Entry, Excel, PowerPoint, Visio, and Phrase, unhealthy actors have been experimenting with various an infection routes to deploy malware.
One such technique seems to be XLL recordsdata, which is described by Microsoft as a “kind of dynamic hyperlink library (DLL) file that may solely be opened by Excel.”
“XLL recordsdata will be despatched by electronic mail, and even with the standard anti-malware scanning measures, customers could possibly open them not figuring out that they might include malicious code,” Cisco Talos researcher Vanja Svajcer mentioned in an evaluation revealed final week.
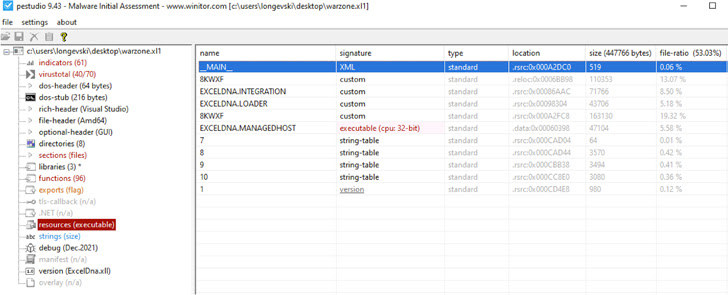
The cybersecurity agency mentioned menace actors are using a mixture of native add-ins written in C++ in addition to these developed utilizing a free device referred to as Excel-DNA, a phenomenon that has witnessed a big spike since mid-2021 and continued to this yr.
That mentioned, the primary publicly documented malicious use of XLL is claimed to have occurred in 2017 when the China-linked APT10 (aka Stone Panda) actor utilized the approach to inject its backdoor payload into reminiscence through course of hollowing.
Different recognized adversarial collectives embody TA410 (an actor with hyperlinks to APT10), DoNot Staff, FIN7, in addition to commodity malware households corresponding to Agent Tesla, Arkei, Buer, Dridex, Ducktail, Ekipa RAT, FormBook, IcedID, Vidar Stealer, and Warzone RAT.
The abuse of the XLL file format to distribute Agent Tesla and Dridex was beforehand highlighted by Palo Alto Networks Unit 42, noting that it “might point out a brand new pattern within the menace panorama.”
“As increasingly more customers undertake new variations of Microsoft Workplace, it’s probably that menace actors will flip away from VBA-based malicious paperwork to different codecs corresponding to XLLs or depend on exploiting newly found vulnerabilities to launch malicious code within the course of area of Workplace functions,” Svajcer mentioned.
Malicious Microsoft Writer macros push Ekipa RAT
Ekipa RAT, in addition to incorporating XLL Excel add-ins, has additionally obtained an replace in November 2022 that permits it to make the most of Microsoft Writer macros to drop the distant entry trojan and steal delicate info.
“Simply as with different Microsoft workplace merchandise, like Excel or Phrase, Writer recordsdata can include macros that may execute upon the opening or closing [of] the file, which makes them attention-grabbing preliminary assault vectors from the menace actor’s perspective,” Trustwave famous.
It is value noting that Microsoft’s restrictions to impede macros from executing in recordsdata downloaded from the web doesn’t prolong to Writer recordsdata, making them a possible avenue for assaults.
“The Ekipa RAT is a superb instance of how menace actors are repeatedly altering their strategies to remain forward of the defenders,” Trustwave researcher Wojciech Cieslak mentioned. “The creators of this malware are monitoring adjustments within the safety business, like blocking macros from the web by Microsoft, and shifting their techniques accordingly.”